Effective Tips for Counterfeit Label Protection Strategies?
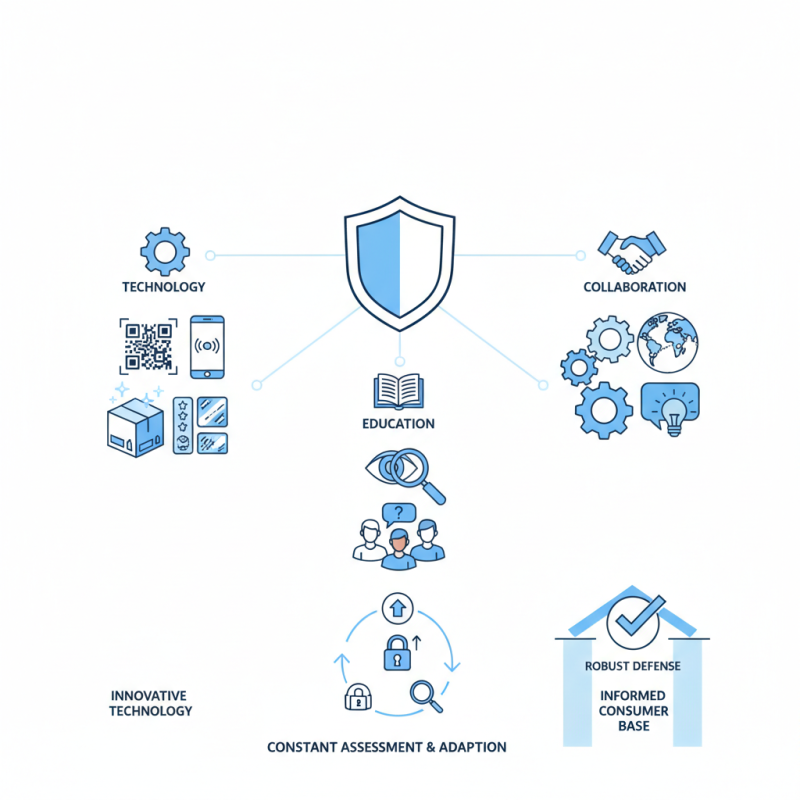
In today's market, counterfeit products have become a significant threat to brands and consumers alike. Protecting against these infringements is vital for maintaining brand integrity and consumer trust. Counterfeit Label Protection strategies are essential in this battle. Companies must adopt a multi-faceted approach that includes technology, education, and collaboration.
Various methods exist to shield genuine products from counterfeiters. High-quality holograms, unique QR codes, and advanced packaging techniques serve as effective deterrents. Yet, while investing in these strategies, businesses should remain vigilant. Counterfeiters continuously evolve, seeking new ways to outsmart protections. Therefore, constant assessment and adaptation of protection measures are crucial.
Moreover, educating consumers about the signs of counterfeit products can empower them. Awareness campaigns can significantly reduce the risk of deception. However, companies often struggle to convey this information effectively. Balancing technical solutions with consumer education is essential. Engaging with customers and fostering a culture of vigilance can enhance counterfeit label protection efforts. Ultimately, creating a robust defense requires not only innovative technology but also a committed and informed consumer base.
Understanding the Importance of Counterfeit Label Protection
Counterfeit label protection is crucial for maintaining brand integrity. Businesses lose billions due to counterfeit products. Understanding the implications can help in formulating effective strategies. Companies must recognize that counterfeit labels undermine customer trust. They can lead to legal issues and damage a brand's reputation.
Implementing robust label protection strategies can mitigate risks. Using advanced technologies is a viable approach. For instance, holograms and QR codes can enhance authenticity. These tools create layers of security that are hard to replicate. However, even with these measures, some businesses falter. They may overlook regular audits or fail to educate employees. This oversight can result in vulnerability, exposing the brand to risks.
Engaging with consumers is also essential. Educating them on how to identify legitimate products fosters trust. Brands should consider community feedback. Listening to customer experiences can highlight potential weaknesses. Furthermore, staying updated on counterfeiting trends can help businesses adapt. This proactive stance ensures a comprehensive approach to label protection.
Identifying Common Types of Counterfeit Labels
Counterfeit labels are a growing issue across various industries. They can undermine brand integrity and mislead consumers. Identifying the types of counterfeit labels is essential for effective protection strategies. Common types include forgery, where labels imitate legitimate products. Another type is the use of recycled materials, which can be hard to distinguish from original packaging.
Advanced technologies often get used in authentic labels. Holograms, QR codes, and unique serial numbers can help verify a product’s legitimacy. However, counterfeiters are becoming increasingly sophisticated. They may produce labels that look nearly identical to authentic ones. This fact makes it necessary for businesses to constantly evaluate their labeling techniques.
It's crucial to train employees about these types of counterfeit labels. They are often the first line of defense. Regular assessments of supply chains are also important. Discrepancies may indicate counterfeiting. These steps help organizations stay vigilant and ensure consumer safety. Recognizing the landscape of counterfeit labeling can lead to more effective strategies.
Effective Technologies for Anti-Counterfeiting Measures
Counterfeit labels pose a significant threat across various industries. To combat this issue, companies are adopting advanced anti-counterfeiting technologies. One effective approach is the use of holograms. These visually striking elements are difficult to replicate and can be customized. Adding specific patterns or colors enhances their uniqueness, making them more reliable.
Another promising technology is the integration of RFID tags. These small devices can store essential product information and are often embedded within the product packaging. They allow for real-time tracking and verification. However, some manufacturers may overlook their security features. This could lead to vulnerabilities that counterfeiters exploit.
Blockchain technology is also emerging as a powerful tool against counterfeiting. By creating tamper-proof records, it increases transparency in supply chains. Yet, implementation can be challenging. Businesses must navigate technical complexities and ensure all parties in the supply chain are on board. While these technologies show great promise, constant evaluation and adaptation are vital. Counterfeiting strategies must stay ahead of emerging threats.
Implementing Comprehensive Training for Staff
Implementing comprehensive training for staff is essential in the fight against counterfeit products. Employees are the first line of defense. They must understand the importance of recognizing and preventing counterfeiting. Effective training will involve detailed content on how to spot fake labels, packaging differences, and verification techniques. Regular workshops and hands-on sessions keep staff engaged and updated.
Utilizing realistic scenarios during training can enhance learning. For example, role-playing exercises can simulate real-life situations. This approach encourages employees to think critically. Yet, there may be resistance or confusion among staff. Some may not see the urgency in learning these skills. Continuous assessment and feedback can address these gaps while fostering a culture of vigilance.
The training should also include effective communication strategies. Staff must feel empowered to report suspicious activity. This creates a supportive environment focused on protection rather than blame. Reflection is crucial; after each training session, discussions on challenges faced can provide insight. Improving training tactics based on feedback will strengthen the overall strategy against counterfeit labels.
Effective Tips for Counterfeit Label Protection Strategies
This chart illustrates the importance of various strategies for counterfeit label protection. Staff training emerges as the most critical, followed closely by technology integration and regular audits, indicating that a multifaceted approach is essential for effective protection against counterfeit labels.
Monitoring and Responding to Counterfeit Threats in the Market
Counterfeit products are a persistent issue in many industries. Monitoring the market for counterfeit threats is crucial. A recent report by the International Anti-Counterfeiting Coalition indicates that counterfeit goods account for nearly $500 billion in lost revenue globally each year. This staggering figure highlights the need for effective strategies to combat counterfeiting.
Companies must implement systems to regularly monitor their products in the market. Using advanced technologies such as blockchain can help ensure product authenticity. A global survey revealed that 60% of businesses integrating technology reported a decrease in counterfeit incidents. Yet, many companies still lack comprehensive strategies to address these threats adequately.
Responding to counterfeit attacks requires agility. Quick action can mitigate damage. Law enforcement collaboration plays a vital role in these efforts. However, many businesses struggle to maintain relationships with law enforcement or have inadequate reporting procedures. Enhancing these areas can lead to more effective responses against counterfeiting threats. Continuous evaluation of existing strategies is essential for improvement.
Effective Tips for Counterfeit Label Protection Strategies
| Strategy | Description | Effectiveness | Implementation Cost |
|---|---|---|---|
| Holograms | Use holographic labels that are difficult to replicate. | High | Medium |
| QR Codes | Implement unique QR codes that can be scanned to verify authenticity. | High | Low |
| Watermarks | Embed invisible watermarks that can be traced. | Medium | Medium |
| Tamper-Evident Seals | Use seals that show visible signs of tampering. | High | Low |
| Serialization | Assign unique serial numbers to each item for tracking. | High | High |
